What’s this all about?
The origin story here is that I wanted to review Hackers, a film I enjoy and Chris describes as “awesome/ly bad”. However, Hackers isn’t science fiction. Well, I could argue that it is set in an alternate reality where computer hackers are all physically attractive with fashionable tastes in music and clothing, but that isn’t enough. The film was set firmly in the present day (of 1995) and while the possibilities of computer hacking may be exaggerated for dramatic purposes, all the computers themselves are quite conventional for the time. (And therefore appear quaint and outdated today.)
With the glorious exception of the three dimensional file storage system on the “Gibson” mainframe. This fantastic combination of hardware and software was clearly science fiction then, and remains so today. While one futuristic element is not enough to justify a full review of Hackers, it did start us thinking. The film Jurassic Park also has a 3D file system navigator, which wasn’t covered in depth by either the book or the online review. And when Chris reached out to the website readers, they provided more examples of 3D file systems being added to otherwise mundane computer systems.
So what we have here is a review of a particular interface trope rather than an entire film or TV show: the three dimensional file browsing and navigation interface.
Scope
This review is specifically limited to interfaces that are recognisably file systems, where people search for and manipulate individual documents or programs. Cyberspace, a 3D representation of the Internet or World Wide Web, is too broad a topic, and better covered in individual reviews such as those for Ghost in the Shell and Johnny Mnemonic.
I also originally intended to only include non-science fiction films and shows but Jurassic Park is an exception. Jurassic Park has been reviewed, both in the book and on the website, but the 3D file system was a comparatively minor element. It is included here as a well known example for comparison.
The SciFiInterfaces readership also provided examples of research papers for 3D file system browsing and navigation—rather more numerous than actual production systems, even today. These will inform the reviews but not be discussed individually.
Because we are reviewing a topic, not a particular film or TV show, the usual plot summaries will be shortened to just those aspects that involve the 3D file system. As a bonus, we can also compare and contrast the different interfaces and how they are used. The worlds of Ghost in the Shell and Johnny Mnemonic are so different that it would be unfair to judge individual interfaces against each other, but for this review we are considering 3D file systems that have been grafted onto otherwise contemporary computer systems, and used by unaugmented human beings to perform tasks familiar to most computer users.
Sources
Having decided on our topic and scope, the properties for review are three films and one episode of a TV show.

Jurassic Park, 1993
“I know this!” and Jurassic Park is so well known that I assume that you do too. We will look specifically at the 3D file system that is used by Lex in the control room to reactivate the park systems.

Disclosure, 1994
This film about corporate infighting includes a virtual reality system, complete with headset, glove, laser trackers, and walking surface, which is used solely to look for particular files.

Hackers, 1995
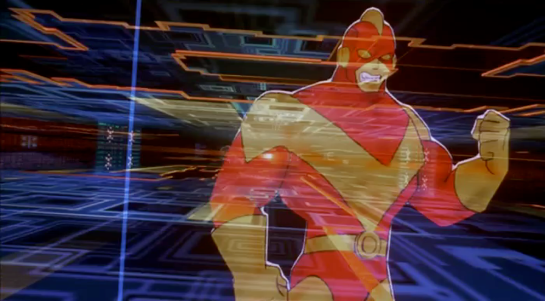
As mentioned in the introduction this film revolves around the hacking of a Gibson mainframe, which has a file system that is both physically three dimensional and represented on computer screens as a 3D browser.

All three of these films date from the 1990s, which seems to have been the high point for 3D file systems, both fictional and in real world research.

Community, season 6 episode 2, “Lawnmower Maintenance and Postnatal Care” (2016)
In this 21st century example, the Dean of a community college buys an elaborate virtual reality system. He spends some of his time within VR looking for, and then deleting, a particular file.

And one that almost made it
File browsing in two dimensions is so well established in general-purpose computer interfaces that the metaphor can be used in other contexts. In the first Iron Man film, at around 52 minutes, Tony Stark is designing his new suit with an advanced 3D CAD system that uses volumetric projection and full body gesture recognition and tracking. When Tony wants to delete a part (the head) from the design, he picks it up and throws it into a trashcan.

I’m familiar with a number of 2D and 3D design and drawing applications and in all of them a deleted part quietly vanishes. There’s no more need for visual effects than when we press the delete key while typing.
In the film, though, it is not Tony who needs to know that the part has been deleted, but the audience. We’ve already seen the design rendering moved from one computer to another with an arm swing, so if the head disappeared in response to a gesture, that could have been interpreted as it being emailed or otherwise sent somewhere else. The trashcan image and action makes it clear to the audience what is happening.
So, that’s the set of examples we’ll be using across this series of posts. But before we get into the fiction, in the next post we need to talk about how this same thing is handled in the real world.