The characters in Johnny Mnemonic make quite a few video phone calls throughout the film, enough to be grouped in their own section on interfaces.
The first thing a modern viewer will note is that only one of the phones resembles a current day handheld mobile. This looks very strange today and it’s hard to imagine why we would ever give up our beloved iPhones and Androids. I’ll just observe that accurately predicting the future is difficult (and not really the point) and move on.
More interesting is the variety of phones used. In films from the 1950s to the 1990s, everyone uses a desk phone with a handset. (For younger readers: that is the piece you picked up and held next to your ear and mouth. There’s probably one in your parents’ house.) The only changes were the gradual replacement of rotary dials by keypads, and some cordless handsets. In 21st century films everyone uses a small sleek handheld box. But in Johnny Mnemonic every phone call uses a different interface.
New Darwin
First is the phone call Johnny makes from the New Darwin hotel.

As previously discussed, Johnny is lying in bed using a remote control to select numbers on the onscreen keypad. He is facing a large wall mounted TV/display screen, with what looks like a camera at the top. The camera is realistic but unusual: as Chapter 10 of Make It So notes, films very rarely show the cameras used in visual communication.
Taxi
The second phone call takes place in Newark, as Johnny rides in a taxi from the airport. Since this is a moving vehicle rather than a room, it shows that wireless videophones also exist. We don’t see how the call is made, just the conversation. Johnny is looking at and speaking into a small screen in front of his seat.

Quick aside: The blue lines at the bottom of the screen are a street map, with the glowing dot being the taxi. While it’s not the focus of this particular interface, it’s interesting that this map seems to be fixed with the indicator moving sideways. Aircraft and now car navigators use a moving map with the indicator moving up for forward. But this is for the passenger rather than the driver so doesn’t need to be particularly useful. And it’s blue, so must be advanced.
At the other end is Ralphie, who is using a desk screen with a keyboard.

We get to see things from Ralphie’s end. His keyboard only has ten keys in two rows of five. Ralphie touches the middle key in the bottom row to end the call.
Is this a dedicated phone rather than a computer? The only full-sized keyboards we see in Johnny Mnemonic are part of systems implied to be outdated or salvaged. Perhaps by 2021 voice recognition is good enough to handle most input. Or perhaps by 2021 status indicators have changed and once again nobody who considers themselves important would have a QWERTY keyboard on their desk, leaving others to do the more “menial” typing.
Shinji’s mobile
There is a cyberspace sequence (discussed in a separate post) during which there is a conversation between a Pharmakom tracker and Shinji, the leader of the Yakuza searching for Johnny, who is in en route by car. Shinji’s phone seems to be just like a current day mobile, if perhaps a little smaller than we’re used to.

Takahashi’s desk phone
Takahashi, head of Pharmakom in Newark, has a desktop screen too. This is a general purpose computer which at various times displays video of his daughter and a corporate database entry about Anna, the Pharmakom founder.

There is no keyboard, but later we will see that the desk surface has hand gesture tracking capability. Here the screen displays an onscreen video phone window and numeric keypad, similar to what we saw in the New Darwin sequence, but Takahashi doesn’t use that interface. Instead he just says “Get me Karl” and the phone dials the recipient automatically.
Takahashi doesn’t prefix his command with a control phrase such as“Siri” or “Computer” which would imply that the computer is always listening. For an executive with a private office this would be reasonable: who else could he be addressing? A second possibility is that the computer does voice recognition and would not respond to commands from anyone else.
Street Preacher’s Phone
As before, the recipient has chosen to show a video splash screen on connection instead of a live video feed.
“Karl” is more commonly known as Street Preacher and works within a church of sorts. We don’t know whether this is genuine religion belief on his part or a cover operation. His phone system is built into a large book, which I thought was intended to be a Bible but Chris identifies as a 16th century ecclesiastical history. There are no controls visible, but we see Karl “pick up” by opening the book so perhaps he “hangs up” by closing it again. Otherwise it could be operated purely by voice.

Public phone
Earlier in the film, Johnny picked up an “Infobahn 3000” handset with built in phone keypad.

His next phone call is from a public phone booth. On screen we see the now familiar videophone keypad. (Apparently this time in cyan, although it’s a very minor color shift.). To the right of the screen are physical buttons, some of which are labelled “start” “stop” and “pause” so perhaps duplicate the onscreen controls. Johnny begins by borrowing Jane’s phone card and swiping it through the payment slot.

The red Infobahn handset is connected to Jane’s card by a cable, although we don’t see Johnny doing this. Johnny types on the handset keypad rather than using the onscreen controls, presumably doing some hacking through the interface.
At first sight it seems unlikely that the phone system could be hacked through an EFTPOS card reader. However there is a long and unhappy history of programmers leaving backdoors and unused functionality in products, often excused with “Well, nobody else knows about it”, which are then exploited. Payment cards themselves often have embedded integrated circuits. This particular hack is not completely implausible.

When the Pharmakom splash screen appears, Johnny types again on the handset. He is manipulating the internal company phone system to gain access to a number that normally would not be available to the public.

The new number connects Johnny to a surprised corporate type who wants to know how Johnny got through.

We’ll learn later on that this gentleman is not at all who he seems to be. For now, note that Johnny talks and listens directly to the screen and speakers in the phone booth, not the handset he is holding.
Spider phone
Just before his brain is scanned by Spider, Johnny tries to make another call. This time he uses a typical 1990s computer CRT display and keyboard. He wears a conventional looking earpiece and microphone, and there is a small camera mounted on top of the display. He types the number on the keyboard and reaches a Pharmakom receptionist, but Johnny is interrupted.

Van call
The last phone call is made by Johnny to Pharmakom again. This time he is in Spider’s van, which doesn’t have a built in phone like the taxi we saw earlier. He uses the handset for audio and a small portable screen for video. There must be a wireless transmitter and receiver somewhere, but it isn’t obvious.


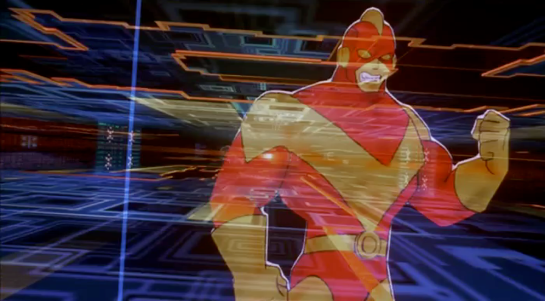
Johnny doesn’t realise that he is actually talking to Takahashi, the head of Pharmakom, through a puppet avatar, which I’ll talk about in the next post.